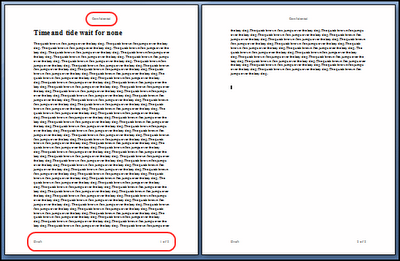
Azure in Pictures: Windows VMs for an application with N-tier architecture
Architecture diagram source: Running Windows VMs for an N-tier architecture on Azure
Elements of the architecture diagram:
- Availability sets. Create an availability set for each tier, and provision at least two VMs in each tier. This is required to reach the availability SLA for VMs.
- Subnets. Create a separate subnet for each tier. Specify the address range and subnet mask using CIDR notation.
- Load balancers. Use an Internet-facing load balancer to distribute incoming Internet traffic to the web tier, and an internal load balancer to distribute network traffic from the web tier to the business tier.
- Jumpbox. Also called a bastion host. A secure VM on the network that administrators use to connect to the other VMs. The jumpbox has an NSG that allows remote traffic only from public IP addresses on a safe list. The NSG should permit remote desktop (RDP) traffic.
- NSGs. Use network security groups (NSGs) to restrict network traffic within the VNet. For example, in the 3-tier architecture shown here, the database tier does not accept traffic from the web front end, only from the business tier and the management subnet.
- SQL Server Always On Availability Group. Provides high availability at the data tier, by enabling replication and failover. Create an availability group listener, and map the listener's DNS name to the IP address of an internal load balancer.
- Active Directory Domain Services (AD DS) Servers. Prior to Windows Server 2016, SQL Server Always On Availability Groups must be joined to a domain. This is because Availability Groups depend on Windows Server Failover Cluster (WSFC) technology.


Comments
Post a Comment